A P2P crypto exchange script is a software package that implements the backend and frontend logic for a noncustodial or semi-custodial peer-to-peer trading platform. Unlike centralized order book exchanges, P2P scripts facilitate direct fiat-to-crypto or crypto-to-crypto transactions between users, with the platform acting as a matching and dispute resolution layer rather than a custodian of all funds. This article examines the core architectural components, escrow mechanics, and operational trade-offs you face when evaluating or deploying such a script.
Core Architecture and Component Stack
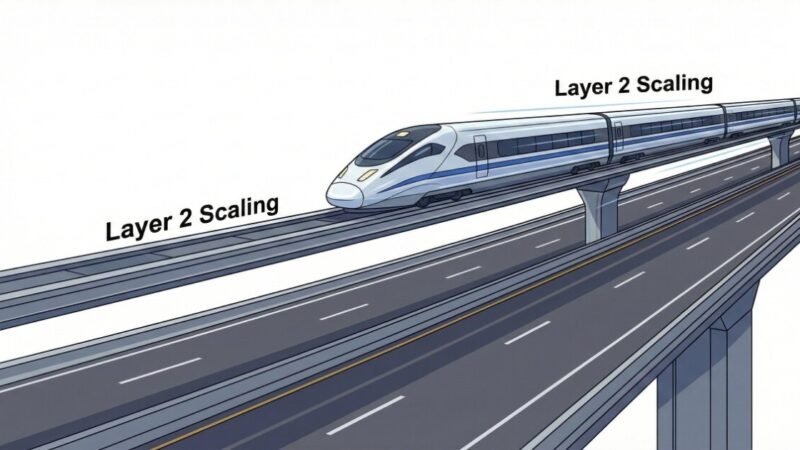
Most P2P exchange scripts deliver three layers: a matching engine that pairs buy and sell offers, an escrow mechanism that holds crypto until both parties confirm the trade, and a dispute resolution workflow that releases funds when payment evidence conflicts arise.
The matching layer typically stores user offers in a database (PostgreSQL or MySQL) indexed by currency pair, payment method, and price. Users post offers with minimum and maximum trade limits, accepted payment rails (bank transfer, mobile money, gift cards), and markup or markdown relative to a reference price feed. The script queries this table to surface compatible counterparties when a taker initiates a trade.
The escrow layer locks the seller’s crypto in a platform-controlled wallet or a smart contract (if building on Ethereum, BSC, or similar chains). For Bitcoin-based scripts, a multisig wallet (2-of-3 or 2-of-2) is common, with keys held by the buyer, seller, and platform. For EVM chains, a Solidity contract implements time-locked escrow with release conditions tied to off-chain confirmation states. The script must track transaction IDs, deposit confirmations, and release signatures across multiple blockchains if supporting multiple assets.
The dispute module logs chat messages, uploaded payment receipts, and user-submitted evidence. When a counterparty flags a trade, the script notifies an admin panel where a human arbiter reviews the timeline, applies platform policy rules, and triggers a partial or full release from escrow. Some scripts expose webhook endpoints for integrating external KYC providers or automated fraud scoring services.
Escrow Mechanics and Release Triggers
Escrow behavior defines the trust model. In a fully noncustodial design, the script generates a multisig address per trade, and both parties must sign a release transaction. The platform holds a third key solely for dispute resolution. This model minimizes platform liability but introduces UX friction, as users must run wallet software capable of multisig signing.
Semi-custodial scripts simplify the flow by holding crypto in a hot wallet controlled by the platform. When the buyer marks payment as sent and the seller confirms receipt, the script broadcasts a withdrawal transaction directly. This reduces latency and simplifies mobile app integration, but concentrates regulatory and operational risk on the platform operator.
Time locks add a fallback. If neither party acts within a configured window (commonly 24 to 72 hours), the script either auto-releases funds back to the seller or flags the trade for admin review. Verify whether the script implements chain-native time locks (CLTV/CSV on Bitcoin, block.timestamp checks on EVM) or relies on cron jobs polling a database state field. The former is trustless but less flexible; the latter allows dynamic policy updates but introduces a synchronization attack surface if the job runner fails.
Payment Rail Integration and Fiat Settlement
P2P exchanges do not process fiat payments directly. Instead, the script presents a UI for users to exchange payment details (bank account numbers, mobile wallet IDs, gift card codes) and upload proof of transfer. The platform verifies nothing except that both parties clicked the confirmation buttons within policy timelines.
This design shifts fraud risk to users. The script should enforce trade limits per user tier to cap exposure. A common pattern: unverified accounts can trade up to $100 equivalent per 24 hour period, KYC-verified accounts up to $5,000, and premium accounts with transaction history exceeding 50 trades and zero disputes may access higher limits. These thresholds live in a configuration table or environment variables; check whether the script exposes an admin UI for adjusting them without code changes.
Some scripts integrate SMS or email verification of payment codes. For example, when a buyer claims to have sent a bank transfer, the script can parse a forwarded confirmation email using regex or an LLM-based classifier, extract the reference number, and auto-flag mismatches. This feature varies widely across vendors and often requires custom tuning per payment provider.
Worked Example: USDT-for-Naira Trade Flow
Alice posts an offer to sell 1,000 USDT (TRC-20) at a 1.5% markup over the Binance NGN rate, accepting Nigerian bank transfers between 50,000 and 500,000 NGN. Bob, holding naira, opens the app, filters for TRC-20 USDT sellers, and selects Alice’s offer. He initiates a trade for 200 USDT.
The script calculates the naira equivalent using the configured oracle (CoinGecko API or a custom weighted index), applies Alice’s 1.5% markup, and displays 200 USDT = 164,600 NGN. Bob confirms. The script instructs Alice to deposit 200 USDT to an escrow address (either a TRC-20 contract or a platform hot wallet). Alice sends the transaction; the script monitors the Tron network via TronGrid or a self-hosted node and awaits six confirmations (roughly 18 seconds on Tron, though you should verify the script’s hardcoded threshold).
Once confirmed, the script displays Alice’s bank details to Bob and starts a countdown timer (default 30 minutes in many scripts). Bob transfers 164,600 NGN via his bank app and uploads a screenshot of the debit alert. He clicks “Payment Sent.” Alice receives a notification, checks her bank account, and clicks “Payment Received.” The script releases the 200 USDT from escrow to Bob’s wallet address.
If Alice disputes the payment, the script freezes the release and notifies the admin panel. An arbiter reviews the chat log, the uploaded screenshot, and Alice’s bank statement (if she provides it). The arbiter either releases to Bob, refunds Alice, or applies a 50/50 split if evidence is inconclusive. The decision triggers a transaction signed by the platform’s escrow key.
Common Misconfigurations and Failure Modes
- Insufficient confirmation depth. Deploying a script that treats one confirmation as final on blockchains with high reorg risk (e.g., ETC, smaller PoW chains) exposes users to double-spend attacks. Verify the default confirmation count per chain in the codebase.
- Hardcoded API keys in version control. Many scripts ship with example .env files containing placeholder keys for price oracles or SMS gateways. Operators who forget to rotate these keys leak rate limits or incur unexpected API charges.
- Missing rate limits on offer creation. Without throttling, a malicious user can spam thousands of fake offers, polluting the order book and degrading search performance. Check whether the script enforces per-user or per-IP limits on POST /offers endpoints.
- Plaintext storage of payment details. Bank account numbers and phone numbers logged in chat tables should be encrypted at rest. Some scripts store this data in varchar columns with no encryption layer, violating GDPR or local privacy regulations.
- No webhook retry logic. If the script sends trade events to an external fraud detection service via webhooks, a temporary network failure can cause missed alerts. Verify whether the script implements exponential backoff or a dead letter queue for failed webhook deliveries.
- Time zone inconsistencies. Scripts that display countdowns in the server’s local time zone confuse users in other regions. Ensure timestamps are stored in UTC and converted client-side using the user’s browser locale.
What to Verify Before You Rely on This
- Current licensing terms of the script (MIT, GPL, proprietary SaaS). Some vendors claim “open source” but restrict commercial use or require revenue sharing.
- Supported blockchain networks and confirmation thresholds. A script advertised as supporting “all ERC-20 tokens” may only include providers for Ethereum mainnet, not L2s or sidechains.
- Escrow wallet architecture (hot vs. cold storage split, multisig scheme, key backup procedures). Ask for a threat model document or disaster recovery runbook.
- Default fee structure. Confirm whether trading fees, withdrawal fees, and dispute resolution fees are hardcoded percentages or configurable per currency pair.
- KYC and AML module maturity. Some scripts ship with placeholder KYC forms that collect data but perform no verification. Verify integration points for third-party providers like Onfido or Sumsub.
- Admin panel access controls. Check whether the script implements role-based permissions (viewer, moderator, super admin) or grants all admin users full database access.
- Update and patch cadence from the vendor. A script last updated in 2021 may contain unpatched vulnerabilities in dependencies (e.g., outdated Express.js, web3.js versions).
- Geographic restrictions or sanctions screening. If your platform will serve global users, confirm whether the script includes IP geofencing or integrates with OFAC/SDN list APIs.
- Database migration strategy. Verify whether schema updates between versions require manual SQL or are handled by an ORM migration tool.
- Documentation quality. A script with sparse or outdated docs will slow your deployment and increase integration errors.
Next Steps
- Deploy a test instance on a private testnet (e.g., Sepolia for Ethereum, testnet for Tron) and execute at least 20 trades covering normal flow, buyer disputes, seller disputes, and timeout scenarios. Log every database state transition.
- Audit the escrow contract or wallet logic with a blockchain security firm if you plan to handle significant volume. Budget for this before launch, not after the first incident.
- Define operational runbooks for common failure modes: oracle downtime, blockchain congestion causing delayed confirmations, mass dispute events during payment system outages. Train your support and admin team on these procedures.
Category: Crypto Exchanges