Crypto exchanges route billions in daily volume through layered systems that handle order matching, custody, settlement, and risk management simultaneously. The technology stack determines latency, failure modes, capital efficiency, and regulatory compliance posture. This article examines the core components of centralized and decentralized exchange architectures, focusing on design decisions that affect execution quality and operational risk.
Order Matching Engine Design
The matching engine sits at the core of exchange performance. Centralized exchanges typically implement in-memory matching engines written in low-latency languages (C++, Rust) that process orders through a limit order book data structure. The engine maintains separate buy and sell trees, often implemented as red-black or AVL trees for O(log n) insertion and deletion.
Order priority follows price-time or pro-rata allocation. Price-time matching awards fills to the oldest order at the best price. Pro-rata distributes fills proportionally across all resting orders at the触发 price level, common in derivatives markets where quote providers expect consistent fill rates.
Matching happens synchronously or asynchronously. Synchronous engines block new order acceptance during match execution, guaranteeing deterministic sequencing but limiting throughput. Asynchronous designs queue incoming orders and process matches in parallel, achieving higher throughput at the cost of potential race conditions during high volatility.
Custody and Settlement Models
Centralized exchanges operate omnibus custody: user deposits flow into exchange-controlled hot and cold wallets. Hot wallets fund immediate withdrawals and inter-exchange transfers. Cold storage holds the majority of assets in air-gapped or hardware-secured wallets, moved to hot wallets through manual or time-locked procedures.
Internal ledger entries represent user balances. Trades settle instantly as database updates; no onchain transaction occurs until withdrawal. This model enables high throughput and supports margin trading by allowing the exchange to net positions internally. The tradeoff is custody risk: users trust the exchange to maintain accurate records and secure private keys.
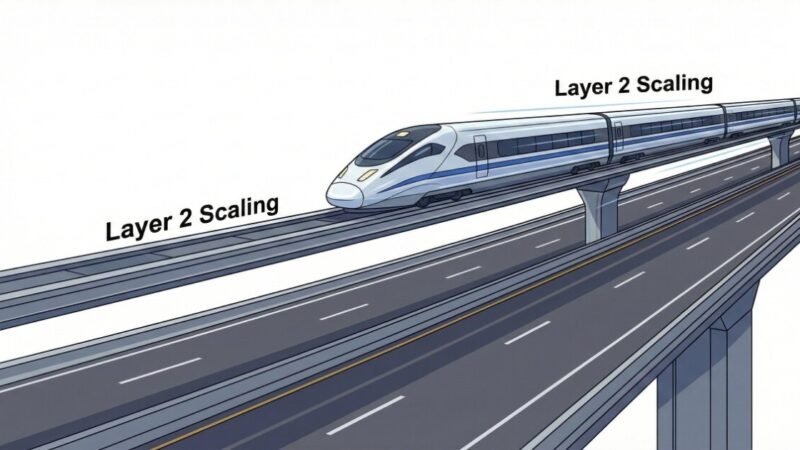
Decentralized exchanges eliminate custody through two architectures. Automated market makers (AMMs) custody liquidity in smart contracts where trades execute against pooled reserves via deterministic pricing formulas. Order book DEXs post orders as onchain state or offchain signed messages, with settlement occurring onchain when a taker accepts terms.
Hybrid models combine offchain matching with onchain settlement. Orders post and match offchain for speed, then settle periodically in batches. This reduces gas costs and increases throughput while maintaining cryptographic proof of execution.
Risk Management Infrastructure
Exchanges implement multiple risk controls to prevent cascading failures. Position limits cap exposure per user and per asset. Margin systems calculate collateral requirements in real time, liquidating positions when maintenance margin falls below thresholds.
Liquidation engines monitor all margined positions continuously. When a position hits liquidation price, the system can close it via market order, transfer it to an insurance fund, or auction it to market makers through a socialized loss mechanism. Design choice affects market impact: immediate market orders create selling pressure; auctions distribute impact but delay resolution.
Circuit breakers halt trading when price moves exceed predefined bands within a time window. Implementation varies: some pause all trading, others restrict only market orders or apply dynamic price limits. The objective is preventing flash crashes while allowing legitimate price discovery.
API rate limits prevent both accidental overload and intentional denial of service. Limits apply per endpoint, per user, and per IP, typically measured in requests per second with burst allowances. WebSocket connections may have separate message rate limits.
Worked Example: Margin Liquidation Flow
A trader holds a 10 BTC long position with 3x leverage, entry price 40,000 USDT, using 133,333 USDT in collateral. Maintenance margin requires 5% of position value. Liquidation triggers when equity falls to (10 × entry price × 0.05) = 20,000 USDT.
BTC drops to 38,666 USDT. Position value becomes 386,660 USDT. Unrealized loss: 13,340 USDT. Equity: 133,333 – 13,340 = 119,993 USDT. Maintenance requirement: 386,660 × 0.05 = 19,333 USDT. Still safe.
BTC continues to 36,666 USDT. Position value: 366,660 USDT. Unrealized loss: 33,340 USDT. Equity: 99,993 USDT. Maintenance requirement: 18,333 USDT. Still safe.
BTC hits 35,333 USDT. Position value: 353,330 USDT. Unrealized loss: 46,670 USDT. Equity: 86,663 USDT. The system miscalculates maintenance as 17,666 USDT due to a rounding error in the price feed aggregation. No liquidation triggers.
BTC drops further to 34,000 USDT. Position now deeply underwater. The exchange must absorb the loss from its insurance fund. This illustrates why price feed precision and calculation rounding matter: a single basis point error in margin calculations compounds across thousands of positions.
Failure Modes and Edge Cases
System overload during volatility creates several failure patterns. Order book depth disappears as makers cancel quotes faster than the engine can process, leaving wide spreads. WebSocket connections drop, causing API clients to miss fills or position updates. Database replication lag means different API nodes serve inconsistent balance data.
Oracle failures affect any exchange using external price feeds for index calculation, funding rates, or liquidation prices. Stale prices can trigger inappropriate liquidations or allow positions to remain open past safe thresholds. Multi-oracle aggregation with outlier filtering mitigates single-source failures but adds latency.
Settlement finality risk appears in DEXs when chains reorganize. A trade confirmed in block N may disappear if that block becomes orphaned. Exchanges typically wait multiple confirmations before crediting deposits, but internal trades may execute before adequate confirmation depth, creating loss scenarios during deep reorgs.
Key management breaches remain the primary catastrophic failure mode for centralized exchanges. Hot wallet compromise allows immediate theft of liquid assets. Cold wallet breaches require defeating multi-signature schemes, time locks, or hardware security modules. Most large-scale thefts exploit operational security rather than cryptographic weaknesses: social engineering, insider access, or supply chain attacks.
Common Mistakes and Misconfigurations
-
Inadequate database indexing on order book queries causes latency spikes under load. Composite indexes on symbol, side, price, and timestamp are essential for sub-millisecond lookups.
-
Missing idempotency keys in order submission APIs allow duplicate orders when clients retry on timeout. Each order should carry a unique client ID that the engine deduplicates.
-
Improper WebSocket reconnection logic causes clients to miss order updates during brief disconnections. Clients must track last received sequence number and request snapshots on reconnect.
-
Liquidation engine using market orders without depth checks creates cascading liquidations when order book is thin. Always verify available liquidity before executing large liquidations.
-
Insufficient price band width on circuit breakers trips frequently during legitimate volatility, training users to ignore halts. Bands should reflect typical intraday ranges for each asset.
-
Cold wallet signing ceremonies without geographic distribution leave all key shards vulnerable to single-location compromise. Separate signers by jurisdiction and physical security domain.
What to Verify Before You Rely on This
- Current margin calculation methodology and liquidation price formula for your positions
- WebSocket message rate limits and reconnection procedures for your trading infrastructure
- Insurance fund size relative to open interest for leveraged products you trade
- Withdrawal processing times and any manual approval thresholds that apply
- KYC and AML verification requirements that may delay first withdrawal
- Maker-taker fee schedule and any volume tier thresholds you approach
- API endpoint uptime SLAs and historical performance during high volatility
- Which price feeds the exchange uses for index calculation and liquidations
- Cold wallet security model: multi-sig threshold, geographic distribution, time locks
- Jurisdiction of legal entity holding custody and applicable regulatory framework
Next Steps
- Review API documentation for your primary exchanges, focusing on WebSocket sequencing and order status transitions to improve client reliability.
- Implement position monitoring that calculates liquidation price independently of exchange APIs, alerting before exchange systems trigger forced closures.
- Test failure scenarios in sandbox environments: simulate WebSocket disconnects, order rejections, and margin calls to validate your risk management logic responds correctly.
Category: Crypto Exchanges